Network Security For Accounting Firms
datasecurity firewalls network security
Technology Understanding Cybersecurity
We’ve written an article before about how to protect your non-cloud assets. In it, we emphasised how Network Security is one of the key non-cloud assets that Accounting firms need to protect.
In a more in-depth look at how to make sure your firm is working with a secure network, we present our 5 tips for working on a secure network. Read on:
1. Make use of firewalls.
What are firewalls? A firewall is a network security system that monitors and controls incoming and outgoing network traffic. As the name conveys, it’s like a fence preventing unsafe connections being made in and out of your networks.
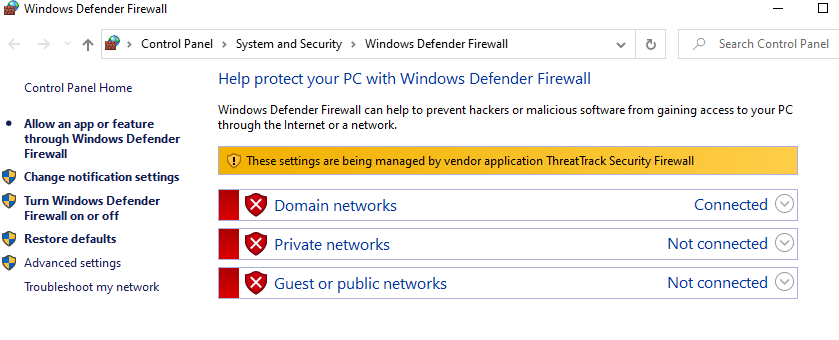
Apple and Windows have free built-in firewalls in their devices. If you’re not sure how to turn yours on, or whether your team has their firewalls turned on, speak to your IT team about it.
2. Make sure you have secure remote access to your office PCs if you or your team are working remote.
Accounting firms have seen the many advantages of remote work in the past years, and we’ve seen some firms go into a remote or hybrid model permanently. With this shift also comes the need to establish that remote teams are accessing client data via secure networks.

Ask your IT Partner about recommendations in securing remote work networks. Steps like logging into VPNs when accessing remote desktops and requiring Two-Factor/Multi-Factor Authentication to access remote desktops are more layers of security around remote work.
For more information about securing data in remote working teams, read our article here.
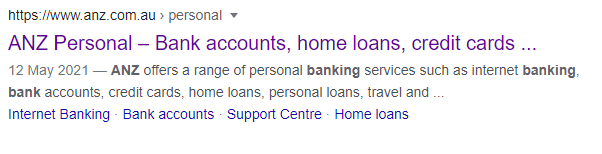
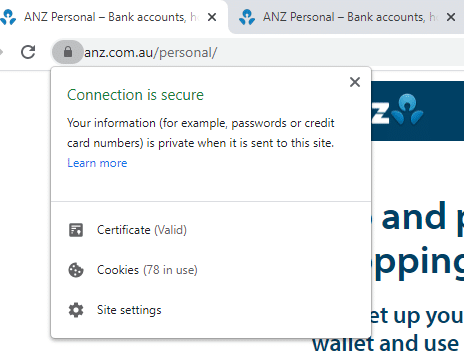
3. When accessing websites, make sure the target address has https in front of it, and has a padlock icon.
Hyper Text Transfer Protocol Secure (HTTPS) is the secure version of HTTP, which is the code over which data is sent from your web browser to the target website you’re going to.
A common phishing trick is to make a website look like a bank or government log-in page with even an identical-looking URL. However, making sure that a website you’re in is an HTTPS one is a step towards network security
4. Educate your team about the danger of public hotspots.
Connecting to public hotspots isn’t recommended as these networks are open to any and all people who can access them. As public hotspots can be accessed for free, you can only imagine how many people are on them.
The better, safer alternative is just using your smartphone as a tethered hotspot. Many carriers let you set your phone up as a secure WiFi hotspot, that you can then access with your laptop.
5. Encrypt files like PDFs with passwords.
Make it a habit to lock files on your computer behind passwords to prevent hackers from accessing them.
If a sensitive file is sent through email, also lock it behind a password. Then, send the password to it through another messaging channel—sending the password in the same email as the file will only defeat the purpose of the password in case of a breach or a compromised email network.

